Navigating the digital landscape demands robust identity checks, especially following breaches like MGM’s, highlighting the need for user education and secure systems.
Current practices often focus on “human verification” rather than true ID authentication, seeking live confirmation to combat bots and fraudulent activities online.
The Growing Importance of Online Identity Verification
The surge in online interactions necessitates increasingly sophisticated identity verification methods. Following significant data breaches, like the one experienced by MGM, organizations are re-evaluating security protocols, yet a knee-jerk reaction isn’t always the optimal solution.
Prioritizing end-user education regarding phishing attempts is crucial, alongside strengthening existing systems. However, the expanding digital footprint and the rise of sophisticated scams demand more proactive measures. Simply removing capabilities from help desks, without addressing underlying vulnerabilities, feels counterproductive, especially when onboarding new users.
The core issue isn’t just verifying an ID’s name (John Smith, for example), but confirming its authenticity – a task challenging for third-party services lacking real-time access to government databases. These services primarily aim for “human verification,” ensuring a live person, not a bot, is involved, which is a critical step in preventing automated fraud and money laundering schemes.
Why ID Verification is Crucial for Security
Robust ID verification is paramount in safeguarding against escalating online threats. The discussed scenario highlights a critical point: if on-premise employee information is compromised via phishing, the security breach extends far beyond simple identity theft. A compromised employee ID signals a systemic vulnerability requiring immediate attention.
Implementing multi-layered security protocols, like requiring full name, department, title, reporting manager, and employee ID upon help desk contact, significantly raises the bar for potential attackers. This initial verification, coupled with secure password reset portals accessed via personal email with expiring codes, minimizes the risk of sensitive information disclosure over the phone.
Ultimately, ID verification isn’t solely about confirming a presented document; it’s about establishing trust and mitigating risk. While third-party services may focus on “human verification” to deter bots, a comprehensive security strategy demands a proactive approach to protecting underlying data and systems from compromise.

Types of ID Verification Methods
Diverse techniques exist, ranging from document checks and biometric scans to knowledge-based questions and multi-factor authentication, bolstering security layers.
Document-Based Verification

Document-based verification remains a cornerstone of ID verification processes, relying on the submission and analysis of official identification documents. This commonly includes verifying the authenticity of driver’s licenses and passports, scrutinizing details against established databases and security features.
However, a critical point arises: many services aren’t truly verifying the ID itself, but rather confirming a “real human” presents a document resembling one. Without real-time access to government databases, verifying authenticity is limited to visual checks and data matching, which can be circumvented with even older, degraded IDs.
National ID card verification offers another avenue, though its prevalence and reliability vary significantly by country. The core challenge lies in ensuring the document is genuine and hasn’t been tampered with, highlighting the need for advanced fraud detection technologies and skilled human review.
Ultimately, document verification serves as an initial layer of security, but its effectiveness is contingent on robust validation methods and awareness of its inherent limitations.
Driver’s License/Passport Verification
Driver’s licenses and passports are frequently utilized for online identity verification due to their widespread acceptance and standardized formats. The process typically involves extracting data from the document – name, date of birth, issuing authority – and cross-referencing it with other data sources.
However, the effectiveness hinges on sophisticated fraud detection. As noted, simply possessing a document matching a name isn’t verification; it’s human presence confirmation. Visual inspection for tampering, holographic features, and microprinting are crucial, but easily bypassed with skilled forgeries.
The age of the document also presents a challenge. An almost decade-old ID with a faded photo, as one example illustrates, can still pass basic checks, highlighting the limitations of purely document-based approaches.
Robust systems combine automated analysis with human review, focusing on anomalies and inconsistencies to mitigate risk and ensure genuine identity confirmation.
National ID Card Verification
National ID card verification mirrors driver’s license/passport checks, relying on data extraction and cross-referencing. However, the specifics vary significantly by country, as national ID formats aren’t globally standardized like passports.
This lack of uniformity complicates automated verification processes, requiring providers to maintain extensive databases and adapt to evolving card designs and security features. The core principle remains the same: confirming the document’s authenticity and matching the presented information.
Like other document-based methods, it’s susceptible to fraud. A valid-looking ID doesn’t guarantee genuine identity, emphasizing the need for layered security. The concern isn’t necessarily the ID itself, but verifying the person presenting it.
Effective systems integrate national ID verification with other methods, such as biometric checks or knowledge-based authentication, to create a more comprehensive and reliable identity confirmation process.
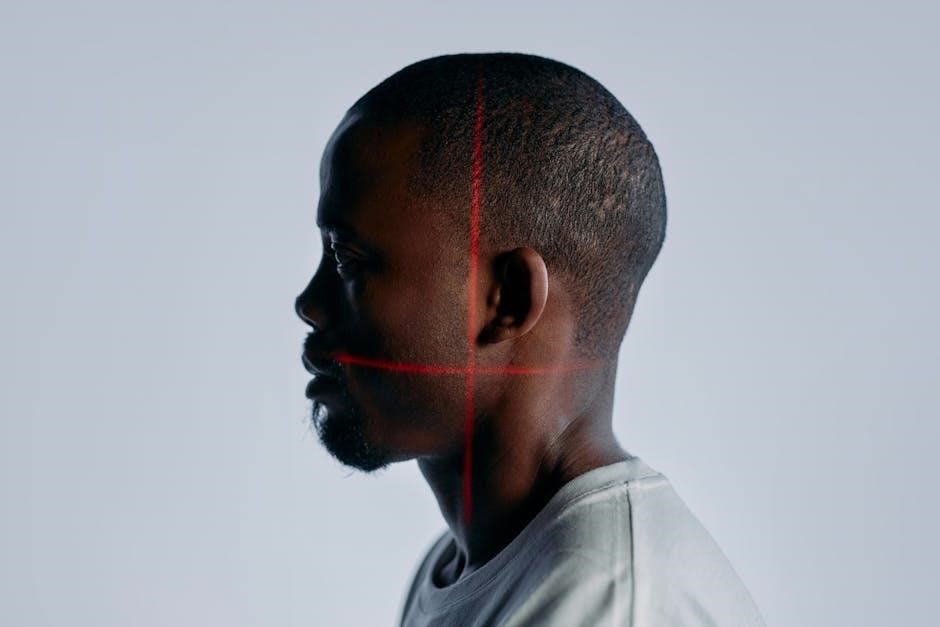
Biometric Verification
Biometric verification utilizes unique biological traits to confirm identity, offering a higher level of assurance than document-based methods alone. It moves beyond “what you have” (an ID) to “who you are,” providing a more robust security layer.
However, it’s crucial to understand that current 3rd party services may primarily focus on confirming a “real human being” rather than definitively verifying the ID itself. The goal is often to deter bots and basic fraud attempts.
The effectiveness hinges on the quality of the biometric data and the sophistication of the matching algorithms. Factors like lighting, image resolution, and variations in facial features can impact accuracy.
Biometric methods are increasingly integrated with other verification techniques to create multi-factor authentication systems, enhancing overall security and reducing the risk of false positives or successful impersonation attempts.
Facial Recognition Technology
Facial recognition is a prominent biometric method, analyzing unique facial features to verify a user’s identity against a stored image or database. It’s widely deployed for ID verification, offering convenience and speed.
However, concerns exist regarding the reliability of these systems, particularly with older or low-quality images. As noted, an ID with a faded or obscured photo can still pass verification, raising questions about true authentication.
The technology relies on algorithms that map facial landmarks, but these can be susceptible to manipulation or spoofing attempts. “Liveness detection” is crucial to prevent the use of photos or videos.
Effectiveness is also impacted by factors like lighting, pose, and expression. Robust systems employ advanced algorithms and multiple checks to mitigate these challenges and ensure accurate identification.
Fingerprint Scanning
Fingerprint scanning, a well-established biometric technique, utilizes the unique patterns of ridges and valleys on a fingertip for identification. It’s a common component of ID verification processes, offering a relatively secure and reliable method.
While highly accurate, fingerprint scanning isn’t foolproof. Factors like skin condition, injury, or the quality of the scanner can affect results. Modern systems employ advanced sensors and algorithms to improve accuracy.
The process involves capturing a fingerprint image, extracting key features (minutiae), and comparing them to a stored template. This comparison determines a match score, indicating the likelihood of a positive identification.
Like facial recognition, fingerprint scanning is vulnerable to spoofing, though advancements in “liveness detection” are addressing this concern. Ensuring the presented fingerprint originates from a live person is critical for security.
Knowledge-Based Authentication (KBA)
Knowledge-Based Authentication (KBA) relies on verifying an individual’s identity through questions only they should know, based on publicly available records or personal history. This method historically involved security questions like “mother’s maiden name” or “first pet’s name.”
However, KBA’s effectiveness has diminished as personal information becomes increasingly accessible through data breaches and social media. Answers to traditional KBA questions are often easily obtainable by malicious actors.
Modern KBA systems are evolving to incorporate more dynamic and challenging questions, drawing from a wider range of data sources. These systems aim to assess not just what you know, but how you know it.
Despite improvements, KBA remains susceptible to social engineering and data compromise. It’s often used as a supplementary verification layer rather than a standalone solution, particularly when combined with other methods.
Two-Factor Authentication (2FA) & Multi-Factor Authentication (MFA)
Two-Factor Authentication (2FA) and Multi-Factor Authentication (MFA) significantly enhance security by requiring users to provide two or more verification factors before granting access. This goes beyond simply knowing a password, adding layers of protection.
Common 2FA methods include one-time codes sent via SMS, authenticator apps (like Google Authenticator), or email verification. MFA expands on this, utilizing three or more factors.
These factors typically fall into three categories: something you know (password), something you have (phone, security key), and something you are (biometrics). Combining these drastically reduces the risk of unauthorized access.
Implementing MFA is crucial, especially given the rise of phishing and password breaches. It’s a proactive step towards safeguarding sensitive information and preventing fraudulent activities, bolstering overall ID verification processes.

The ID Verification Process: A Step-by-Step Guide
The process involves data submission, document uploads, real-time checks, liveness detection, and ultimately, a verification result – ensuring secure access and trust.
Step 1: Data Collection & Submission
Initiating ID verification begins with a carefully structured data collection phase. This typically involves requesting fundamental personal information from the user, such as their full legal name, date of birth, current address, and potentially, their contact details like email and phone number.
The importance of accuracy cannot be overstated; discrepancies between submitted data and the information on the provided identification document will likely trigger flags and delays in the verification process. Organizations must clearly communicate the required data points to users, ensuring a smooth and efficient submission experience.
Furthermore, secure data transmission is paramount. Utilizing encrypted connections (HTTPS) and adhering to data privacy regulations (like GDPR or CCPA) are crucial to protect sensitive user information during submission. A well-defined submission process sets the foundation for a reliable and trustworthy ID verification workflow, mirroring practices like those used for password resets via secure portals.

Step 2: Document Upload & Image Quality
Following data submission, users are prompted to upload images of their identification documents; Commonly accepted documents include driver’s licenses, passports, and national ID cards. The upload process must be user-friendly, supporting various image formats (JPEG, PNG) and offering clear instructions.
However, successful verification heavily relies on image quality. Blurry, pixelated, or partially obscured images are often rejected. Systems should provide real-time feedback to users regarding image quality, guiding them to retake the photo if necessary. This proactive approach minimizes delays and frustration.
Organizations should also implement measures to prevent fraudulent uploads. This includes checking file sizes, validating image metadata, and potentially employing image analysis techniques to detect tampering. Ensuring clear, unaltered document images is vital, as simply verifying a name against an ID doesn’t guarantee authenticity without assessing the document itself.
Step 3: Real-Time Verification Checks
Once a document is uploaded, the ID verification system initiates a series of real-time checks. These checks go beyond simply confirming the name on the ID; they aim to validate the document’s authenticity and prevent fraud. This often involves cross-referencing information against various databases, though direct access to government databases is typically limited for third-party services.
Instead, verification focuses on identifying inconsistencies and anomalies. This includes checking for valid document formats, security features (holograms, watermarks), and comparing data points against known patterns. The system assesses whether the ID appears genuine, even if it can’t definitively confirm its validity with a government source.
Crucially, these checks are designed to verify the presence of a real person, not necessarily the absolute truthfulness of the ID itself. The goal is to deter bots and scammers, ensuring a human is behind the interaction, rather than a sophisticated, automated attack.
Step 4: Liveness Detection & Anti-Spoofing Measures
A critical component of modern ID verification is ensuring the person presenting the ID is physically present and a live human being. This is achieved through liveness detection, employing techniques to prevent the use of photos, videos, or sophisticated deepfakes.
Common methods include requesting specific movements – blinking, smiling, or head turns – that are difficult to replicate with static images or pre-recorded videos. Advanced systems analyze micro-expressions and subtle facial cues to confirm genuine liveness.
Anti-spoofing measures also address presentation attacks, where someone attempts to deceive the system with a realistic replica of an ID or face. These systems analyze image quality, lighting, and reflections to detect anomalies indicative of a spoofing attempt. Ultimately, the aim is to confirm a real, live person is interacting with the system, bolstering security against fraudulent access.
Step 5: Verification Results & Outcomes
Following the completion of verification checks, a definitive result is generated, typically categorized as ‘verified’, ‘unverified’, or ‘pending review’. A ‘verified’ outcome grants access or enables the desired service, signifying successful identity confirmation.
An ‘unverified’ result indicates discrepancies or failures during the process, potentially stemming from document issues, liveness detection failures, or data mismatches. This often triggers further investigation or requests for additional information.
‘Pending review’ signifies the need for manual assessment by a human agent, particularly when automated systems are inconclusive. Organizations must clearly communicate outcomes to users, providing explanations for rejections and guidance on resolution. Transparent communication builds trust and minimizes user frustration, while robust audit trails document the entire verification journey for compliance purposes.

Challenges and Concerns with ID Verification
Privacy risks, false positives, and the evolving threat of deepfakes pose significant hurdles. Reliance on third-party services also introduces limitations and potential vulnerabilities.
Privacy Concerns and Data Security
The collection and storage of sensitive personal data during ID verification processes raise substantial privacy concerns. Users understandably worry about how their information – including images of government-issued IDs and biometric data – is being handled, secured, and potentially shared.
Data breaches represent a significant threat, as compromised ID information can lead to identity theft and other malicious activities. Organizations must implement robust security measures, including encryption and access controls, to protect this data.

Transparency is crucial; individuals should be clearly informed about what data is being collected, how it will be used, and with whom it might be shared. Compliance with data privacy regulations, such as GDPR and CCPA, is paramount. Furthermore, minimizing data retention periods and employing data anonymization techniques can help mitigate privacy risks.
False Positives and Accessibility Issues
ID verification systems aren’t foolproof and can generate false positives, incorrectly flagging legitimate users as fraudulent. This can lead to frustrating experiences and denied access to essential services, particularly impacting vulnerable populations.
Accessibility presents another challenge. Individuals may lack access to the required technology – a smartphone with a camera, reliable internet connectivity – or may have disabilities that hinder their ability to complete the verification process.
Older identification documents, like those nearing expiration or with faded images, can also cause verification failures, even if the ID is valid. Organizations must offer alternative verification methods and provide clear support channels to address these issues, ensuring inclusivity and minimizing barriers to access. A robust appeal process for wrongly flagged users is also essential.
The Rise of Deepfakes and Synthetic IDs
A significant emerging threat to ID verification is the proliferation of deepfakes and synthetic identities. Advanced AI technologies now enable the creation of highly realistic, yet entirely fabricated, identification documents and convincing video impersonations.
These synthetic IDs can bypass traditional verification methods that rely on document authenticity checks or even basic facial recognition, as they present seemingly valid information and appearances. The ability to create convincing forgeries poses a serious risk to security and increases the potential for fraud.
Combating this requires sophisticated anti-spoofing measures, including liveness detection that goes beyond simple movement checks, and continuous monitoring for patterns indicative of synthetic identity creation. Verification providers must constantly evolve their techniques to stay ahead of these increasingly sophisticated threats.
Limitations of Third-Party Verification Services
While offering convenience, relying solely on third-party ID verification services presents inherent limitations. A critical concern is the lack of direct access to primary data sources like government databases, hindering true authentication.
Many services primarily perform “human verification,” confirming a real person is present rather than validating the ID’s legitimacy. This is illustrated by instances where outdated or poor-quality IDs successfully pass verification checks, raising questions about effectiveness.
Furthermore, the scope of verification can vary significantly between providers, and their databases may not be comprehensive or up-to-date. Organizations must carefully evaluate a provider’s capabilities and understand the potential for false positives or failures, supplementing with internal security protocols.

Best Practices for Implementing ID Verification
Prioritize robust provider selection, ensuring compliance with KYC/AML regulations, and comprehensive employee training alongside continuous system monitoring for optimal security.
Choosing the Right ID Verification Provider
Selecting an ID verification provider requires careful consideration, moving beyond the perception that many services merely perform “human verification” instead of authenticating documents. A crucial aspect is determining if the provider offers genuine document verification capabilities, or simply confirms a real person is present.
Look for providers demonstrating access to reliable data sources, though direct access to government databases is unlikely, assess their methods for confirming ID validity. Evaluate their technology suite – do they offer document-based checks, biometric options, or knowledge-based authentication? Consider scalability; can the provider handle your current and projected verification volumes?
Prioritize providers with strong security protocols and a commitment to data privacy, especially given concerns around sensitive personal information. Review their compliance certifications (SOC 2, GDPR, etc.). Finally, assess their pricing model and ensure it aligns with your budget and verification needs. Don’t solely focus on cost; prioritize accuracy and reliability.
Compliance with Regulations (KYC/AML)
Robust ID verification is fundamental to complying with Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations, particularly crucial in financial services and increasingly relevant across various sectors. These regulations aim to prevent illicit financial activities and ensure transparency.
Effective ID verification processes help organizations establish customer identities, assess risk profiles, and monitor transactions for suspicious behavior. Providers should demonstrate understanding of relevant jurisdictional requirements, as KYC/AML standards vary globally. Documentation of verification procedures is essential for audits and regulatory reporting.
Beyond initial verification, ongoing monitoring is vital. Regularly update ID verification systems to reflect evolving regulatory landscapes and emerging fraud techniques. Implement procedures for re-verifying customers periodically, especially those deemed high-risk. Failure to comply can result in substantial fines and reputational damage.
Employee Training and Internal Protocols
Comprehensive employee training is paramount for successful ID verification implementation. Staff handling verification processes must understand the importance of data security, privacy regulations, and the nuances of different ID document types. Training should cover identifying fraudulent documents and recognizing red flags indicative of potential identity theft.
Establish clear internal protocols for handling sensitive customer data. Limit access to verification information on a need-to-know basis and enforce strict data handling procedures. Implement a system for escalating suspicious cases to a dedicated security team. Regularly review and update protocols to address emerging threats.

Emphasize the importance of verifying identity before providing access to sensitive information or systems. As highlighted, a simple employee ID check can significantly bolster security, especially against phishing attempts. Document all verification steps and maintain detailed audit trails for accountability.
Ongoing Monitoring and System Updates
Continuous monitoring of the ID verification system is crucial for maintaining its effectiveness. Regularly analyze verification data to identify trends, detect potential vulnerabilities, and assess the performance of chosen methods. Track false positive and false negative rates to refine verification parameters and improve accuracy.
Stay abreast of evolving fraud techniques, such as deepfakes and synthetic IDs. The landscape of identity theft is constantly changing, necessitating frequent system updates and the integration of new anti-spoofing measures. Prioritize solutions offering liveness detection and robust image analysis capabilities.
Regularly update third-party verification services and internal protocols. Ensure compliance with evolving KYC/AML regulations and data privacy standards. Proactive system maintenance and adaptation are essential for mitigating risks and safeguarding against emerging threats, as seen with recent breaches.
